Playing Trick and No Treat with Malicious Apps | Cyware Hacker News

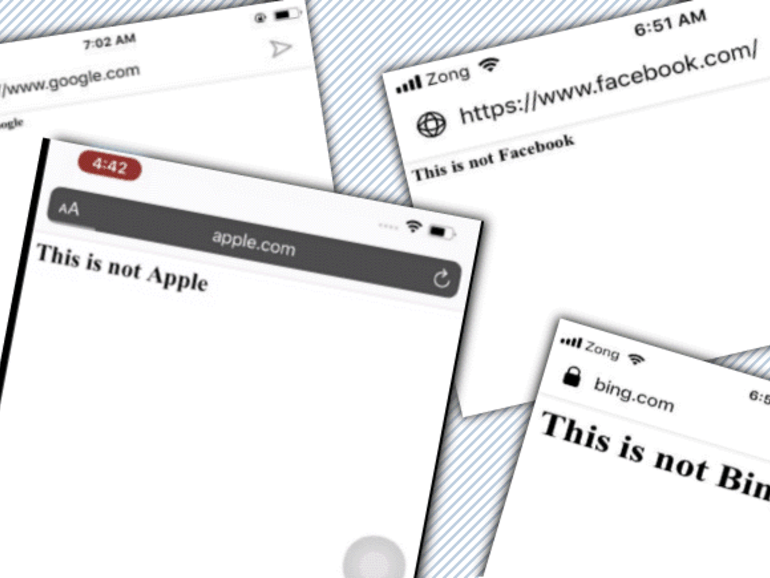
Past thirty day period, researchers spotted 17 Android applications infected with the Joker trojan in Google Participate in Retail outlet. These malicious applications posed as utility services applications to bypass the Google Enjoy vetting approach.